Cybersecurity Explainer Video Maker
Turn complex security concepts into clear, engaging videos in minutes. Agent Opus is a cybersecurity explainer video maker that transforms your prompts, scripts, or blog posts into publish-ready videos with AI motion graphics, professional voiceover, and dynamic visuals. No timeline, no manual editing—just describe your security topic and get a finished video optimized for LinkedIn, YouTube, or internal training. Perfect for security teams, SaaS founders, and marketers who need to explain threats, compliance, or product features without hiring a production crew.
Explore what's possible with Agent Opus
Reasons why creators love Agent Opus' Cybersecurity Explainer Video Maker
Skip the Studio Costs
Create broadcast-quality cybersecurity videos without hiring crews, renting space, or waiting weeks for post-production.
Build Trust Instantly
Deliver polished, professional explainers that position your brand as the authority clients turn to for cybersecurity guidance.
Complex Topics Made Clear
Turn intricate security concepts into visuals anyone can grasp, so your audience actually understands the risks and solutions.
Stay Ahead of Threats
Publish timely explainers on emerging vulnerabilities and attacks faster than competitors can schedule a shoot.
Scale Your Reach Effortlessly
Produce dozens of tailored explainers for different audiences, platforms, and threat scenarios without multiplying your workload.
Consistent Brand Voice
Every explainer sounds and looks like your team, reinforcing recognition and credibility across all your security content.
How to use Agent Opus’ Cybersecurity Explainer Video Maker
 1
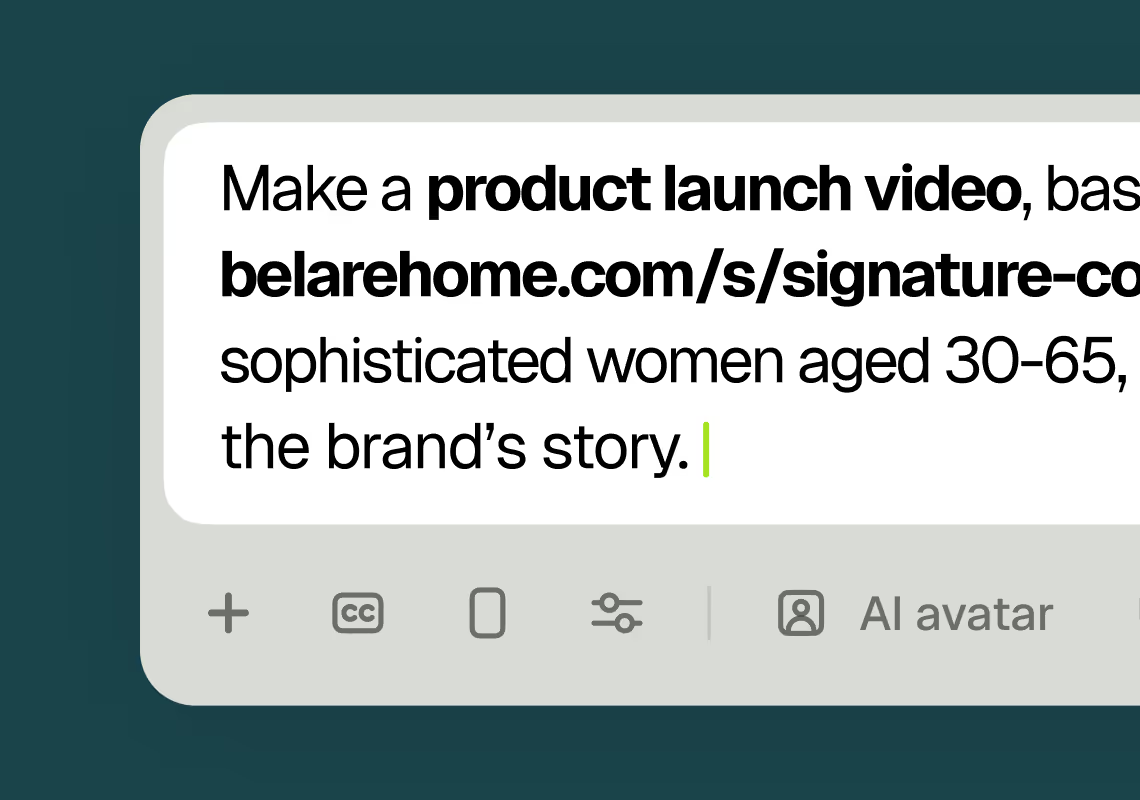
1Describe your video
Paste your promo brief, script, outline, or blog URL into Agent Opus.
 2
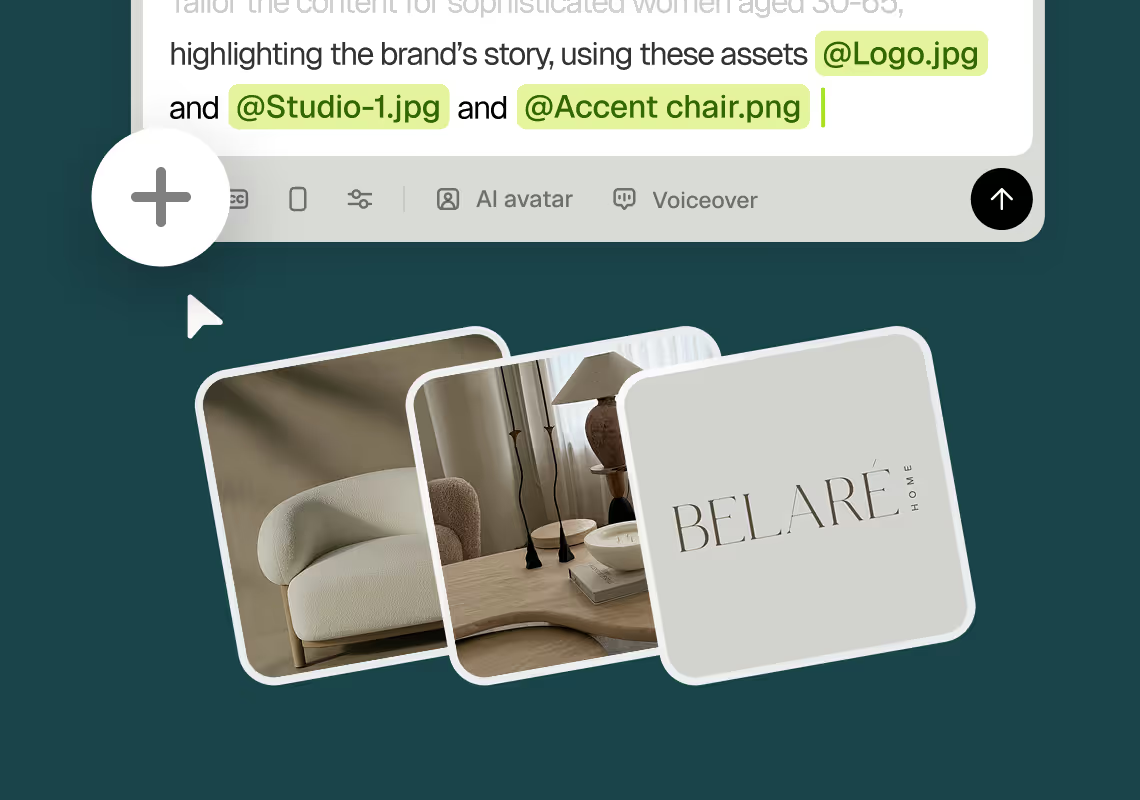
2Add assets and sources
Upload brand assets like logos and product images, or let the AI source stock visuals automatically.
 3
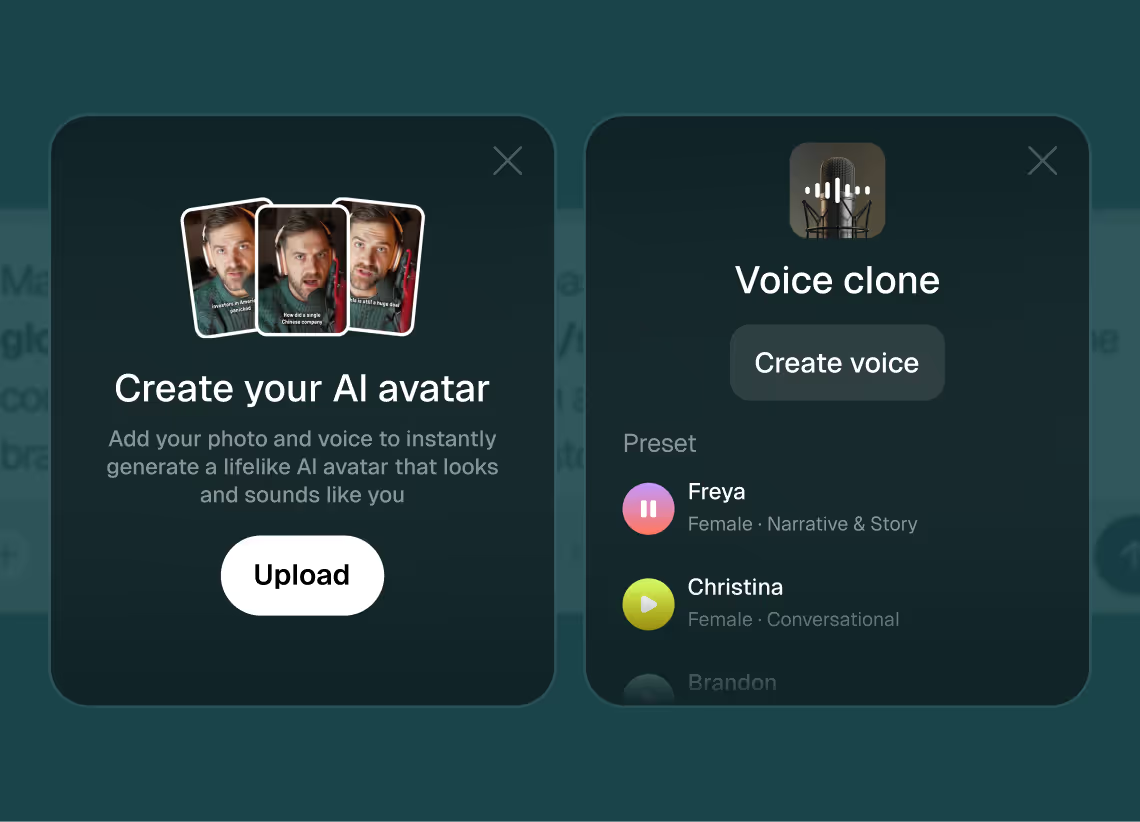
3Choose voice and avatar
Choose voice (clone yours or pick an AI voice) and avatar style (user or AI).
 4
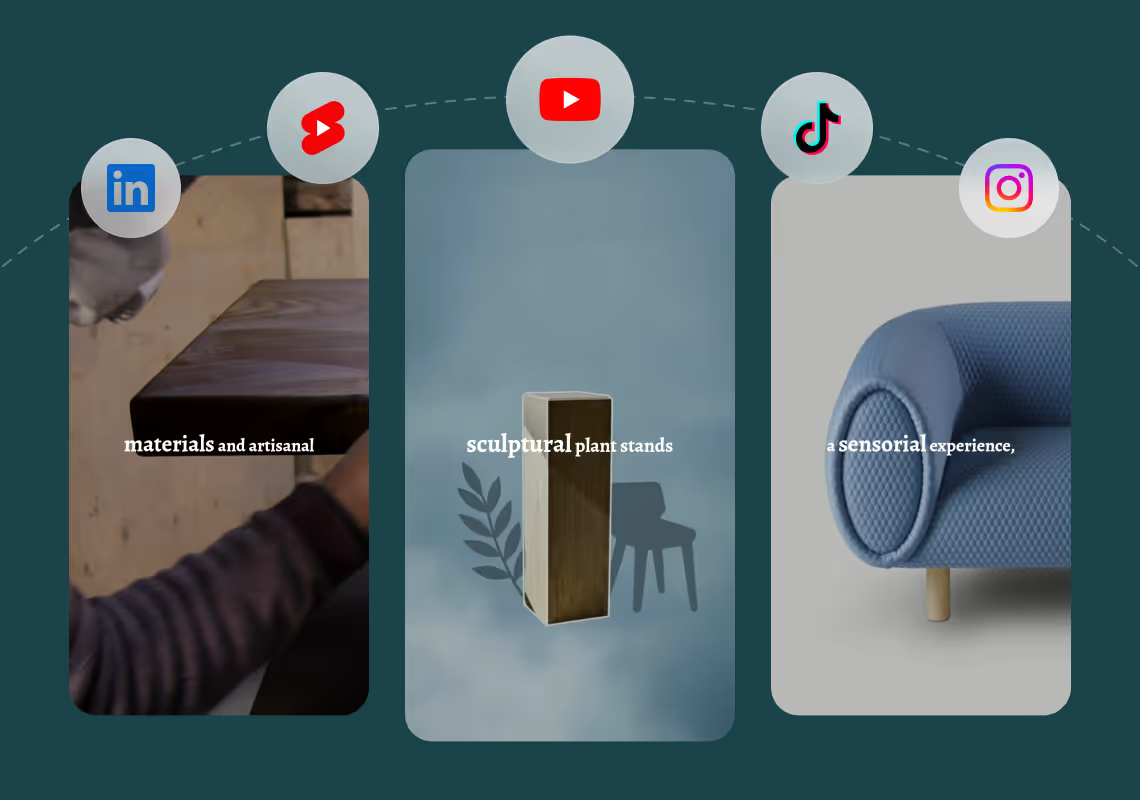
4Generate and publish-ready
Click generate and download your finished promo video in seconds, ready to publish across all platforms.
8 powerful features of Agent Opus' Cybersecurity Explainer Video Maker
Technical Concept Breakdown
Transform complex encryption, firewall logic, and authentication flows into clear visual explainers automatically.
Security Protocol Animations
Create step-by-step videos demonstrating VPN setup, two-factor authentication, and password hygiene from prompts.
Incident Response Walkthroughs
Turn breach response plans and security playbooks into training videos with automated narration and graphics.
Threat Scenario Visualization
Generate animated sequences showing phishing attacks, malware spread, and breach scenarios from text descriptions.
Risk Assessment Summaries
Convert vulnerability reports and penetration test findings into executive-ready video summaries with AI narration.
Network Diagram Animation
Visualize firewall architectures, zero-trust models, and network segmentation concepts as animated explainer videos.
Compliance Training Videos
Generate GDPR, HIPAA, and SOC 2 explainer content with on-brand visuals from regulatory text inputs.
Awareness Campaign Content
Produce social engineering awareness and safe browsing videos from security awareness scripts in minutes.
Testimonials
This looks like a game-changer for us. We're building narrative-driven, visually layered content — and the ability to maintain character and motion consistency across episodes would be huge. If Agent Opus can sync branded motion graphics, tone, and avatar style seamlessly, it could easily become part of our production stack for short-form explainers and long-form investigative visuals.
srtaduck
I reviewed version a and I was very impressed with this version, it did very well in almost all aspects that users need, you would only have to make very small changes and maybe replace one of 2 of the pictures, but even saying that it could be used as is and still receive decent views or even chances at going viral depending on the story or the content the user chooses.
Jeremy
all in all LOVE THIS agent. I'm curious to see how I can push it (within reason) Just need to learn to get the consistency right with my prompts
Rebecca
Frequently Asked Questions
How does a cybersecurity explainer video maker handle technical scripts versus short prompts?
Agent Opus adapts to both extremes. If you paste a 2,000-word whitepaper on zero-trust architecture, the system parses key concepts, identifies logical scene breaks, and generates a structured explainer with animated diagrams for each principle—segmentation, least-privilege access, continuous verification. It auto-sources network topology visuals, applies motion graphics to illustrate data flows, and paces the narration so technical details land without overwhelming viewers. Conversely, if you submit a three-sentence prompt like 'Explain phishing attacks to non-technical employees,' Agent Opus expands that into a complete script, sources email UI mockups and warning-sign iconography, and delivers a 60-second video ready for Slack or onboarding decks. The cybersecurity explainer video maker uses natural language processing to detect whether your input is a detailed compliance brief or a high-level concept, then adjusts scene density, visual complexity, and voiceover speed accordingly. For maximum control, provide a bulleted outline with specific examples—'Scene 1: attacker sends fake invoice; Scene 2: employee clicks link; Scene 3: credentials stolen'—and Agent Opus will animate each beat with relevant stock footage, AI motion graphics for data exfiltration, and a professional voiceover that emphasizes the human error without sounding preachy. The result is a publish-ready explainer that matches your input's depth, whether you're training a board of directors or educating frontline support staff.
What are best practices for prompts in a cybersecurity explainer video maker to ensure clarity and engagement?
Start with a clear objective and audience definition. Instead of 'Make a video about ransomware,' write 'Explain ransomware attack stages to small-business owners who have no IT background—cover initial infection, encryption, ransom demand, and recovery options.' This tells the cybersecurity explainer video maker to use plain language, avoid acronyms, and prioritize visual metaphors over technical diagrams. Next, structure your prompt with logical sections: 'Intro: define ransomware in one sentence. Body: show how it spreads via phishing email, encrypts files, and locks systems. Conclusion: highlight backup strategies and incident-response steps.' Agent Opus will generate distinct scenes for each section, apply appropriate pacing, and source visuals like padlock icons, email screenshots, and backup-server imagery. If you want specific examples, include them: 'Use the WannaCry attack as a case study' or 'Show a healthcare organization losing patient records.' The system will pull relevant news imagery or create animated reenactments. For voiceover tone, specify 'authoritative but approachable' or 'urgent and action-oriented'—Agent Opus adjusts narration speed and inflection accordingly. If you have brand assets, mention them: 'Feature our company logo in the intro, use our blue-and-white color scheme, and include a screenshot of our security dashboard in the solution section.' Finally, define your output format: 'Vertical video for LinkedIn, 90 seconds max, with captions burned in for sound-off viewing.' The cybersecurity explainer video maker will optimize aspect ratio, trim unnecessary detail, and ensure every frame reinforces your key message. Avoid vague prompts like 'cybersecurity video'—the more context you provide about audience, goal, and structure, the more precise and effective your explainer will be.
Can a cybersecurity explainer video maker keep on-brand voices, logos, and visuals across multiple videos?
Yes, and this is critical for security teams producing ongoing training content or SaaS companies building a video library. Agent Opus supports voice cloning, so you record a 30-second sample of your CISO or security lead reading a script, and the cybersecurity explainer video maker replicates that voice across every video you generate. This ensures consistency—viewers recognize the same authoritative voice explaining phishing, malware, and compliance updates, which builds trust and reinforces your brand identity. For logos and visual assets, upload your brand kit once: company logo, product screenshots, approved color palette, and any custom icons or diagrams. Agent Opus stores these assets and automatically integrates them into every explainer. If you generate a video on multi-factor authentication today and another on data encryption next week, both will feature your logo in the intro, use your brand colors for motion graphics, and include screenshots of your actual security dashboard rather than generic stock imagery. This eliminates the manual work of re-uploading assets or briefing a new designer each time. The system also learns from your feedback—if you prefer certain visual styles, pacing, or terminology, those preferences carry forward. For example, if your first video uses the term 'threat actor' instead of 'hacker,' and you approve that choice, future videos will default to your preferred language. This brand consistency is especially valuable for compliance training libraries, where employees need to recognize your organization's voice and visual identity across dozens of modules. The cybersecurity explainer video maker becomes an extension of your brand team, ensuring every video—whether it's a 60-second LinkedIn post or a 10-minute internal training—looks and sounds like it came from the same professional production house, even though you're generating them on demand from text prompts.
What are the limitations or edge cases of a cybersecurity explainer video maker when handling highly technical or regulated content?
Agent Opus excels at translating complex security concepts into visual narratives, but certain scenarios require human oversight. First, highly specialized compliance content—like HIPAA breach notification timelines or GDPR data-processing agreements—may need legal review before publication, even if the video is technically accurate. The cybersecurity explainer video maker generates content based on your input, so if your script contains outdated regulations or misinterprets a compliance requirement, the video will reflect that error. Always have a subject-matter expert review explainers that will be used for official training or customer-facing compliance documentation. Second, proprietary security architectures or confidential incident details require careful prompt crafting. If you paste an internal post-mortem report with sensitive IP addresses, vendor names, or unpatched vulnerabilities, Agent Opus will visualize that information—so sanitize your input first or use placeholder terms. The system does not automatically redact confidential data. Third, extremely niche technical concepts—like zero-day exploit chains or advanced persistent threat tactics—may require supplemental visuals you provide. While Agent Opus auto-sources stock imagery and generates motion graphics, it cannot create bespoke 3D renderings of your custom network topology or animate a novel attack vector that has no visual precedent. In those cases, upload your own diagrams or screenshots, and the cybersecurity explainer video maker will integrate them into the final video. Fourth, real-time or breaking-news content has a knowledge cutoff. If a new ransomware variant emerged yesterday, Agent Opus may not have imagery or context for it yet—you will need to describe it explicitly in your prompt or provide reference links. Finally, accessibility and localization: the system generates videos in English by default with AI voiceover, but if you need multilingual explainers or specific accessibility features beyond standard social-platform captions, plan for post-generation adjustments or specify those requirements upfront. Despite these edge cases, the cybersecurity explainer video maker handles the vast majority of security education content—phishing awareness, password hygiene, incident response, compliance overviews, product security features—with minimal human intervention, freeing your team to focus on strategy and review rather than production logistics.
