Linux MDM Software in 2026: What It Is, Why It Matters
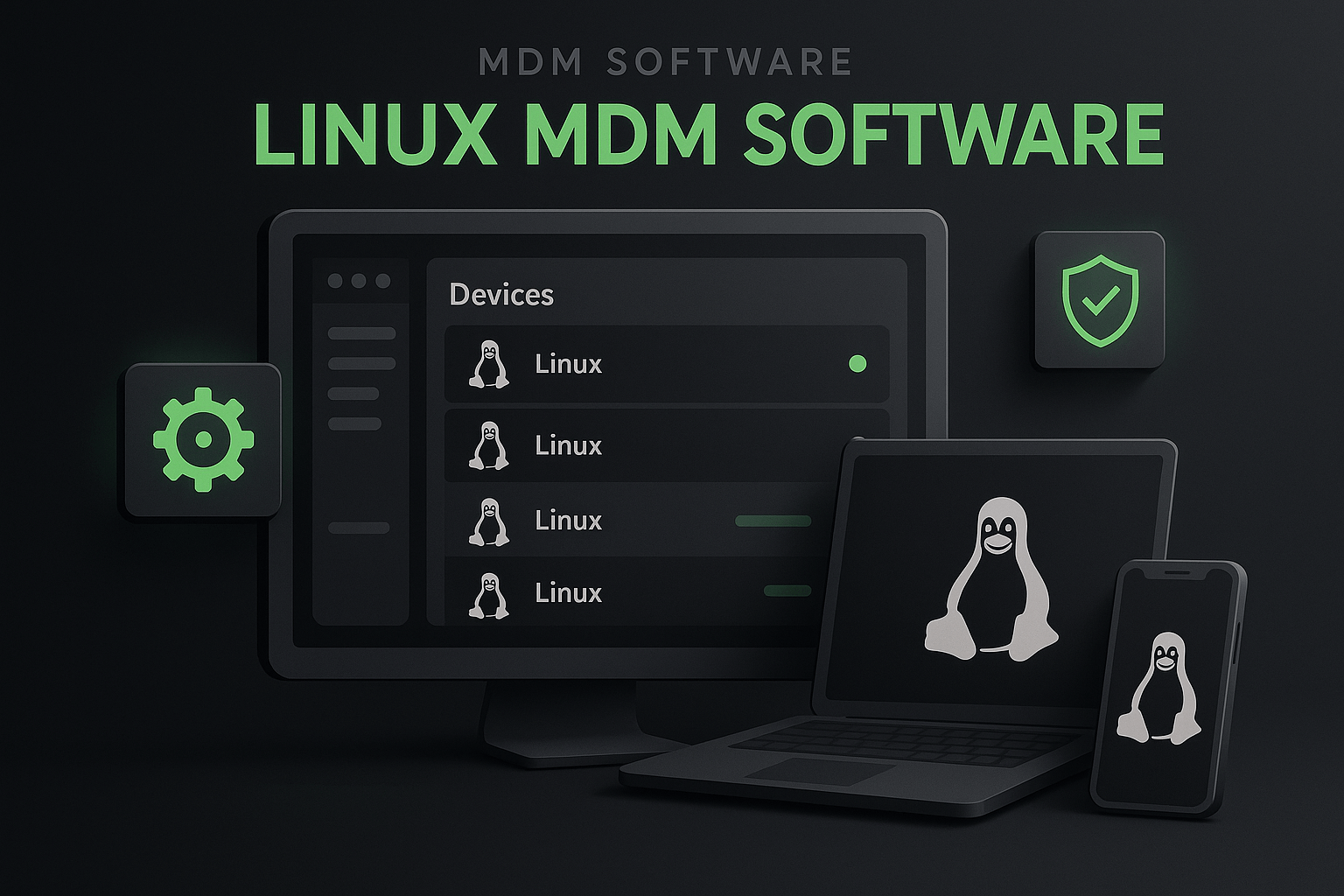
Mobile device management for Linux isn’t a future trend anymore. It’s something real that IT teams have to deal with a lot today. If you’re running fleets of Linux laptops, servers, kiosks, or embedded devices, you will sooner or later need tooling that keeps them configured, secure, and compliant. This isn’t “nice to have.” It's the core infrastructure for your dev team.
Linux device management tools often called Linux MDM software let you manage, monitor, update, and secure your Linux endpoints from a central console. That means you’re not hand-typing config commands on 50 machines. You’re not patching by hand. You’re not scrambling when a security team screams about compliance. With the right MDM, you can automate those parts that are repetitive and error-prone.
Below is a practical list of tools you should be thinking about. For each, I’ll explain what it does, when to use it, how it’s done, common mistakes to avoid, and what happens if you get it wrong.
1) Swif’s Unified Linux MDM (Enterprise Grade)
Why it’s first: Swif.ai is built as a unified enterprise mobile device management that covers Linux alongside Windows, macOS, iOS, and Android, so it works in all mixed environments.
Linux support isn’t an afterthought here. Swif really shines in Linux, offering the widest support for all Linux OS’s such as Ubuntu, Arch Linux, Debian, Universal Blue and more.
What it does
Swif.ai gives you:
- Centralized visibility and control over your Linux devices
- Compliance automation and policy enforcement
- Remote access and troubleshooting
- Reporting and auditing you can plug into governance workflows
That last bit matters the most, it’s not just management, it’s risk reduction.
When to use it
If you’re in a regulated environment (SOC2, ISO27001, HIPAA), you have to demonstrate config control and audit trails. Swif.ai includes predefined compliance patterns and helps enforce them automatically. This saves time and headaches when auditors come knocking. They are also Vanta, Drata and Thoropass partners, so they can handle automated evidence retrieval by the auditors.
If you have a mixed fleet (Linux + others), using a single solution is less brittle than separate platforms for each OS.
How it works
Swif.ai installs lightweight agents on your Linux machines. Those agents report back to the central console. You define policies centrally, such as “ensure disk encryption is enabled” or “block SSH except on approved ports” then Swif.ai checks and enforces those across all devices.
You can also do remote support tasks without needing a VPN into the network.
Common mistakes people make
- Thinking MDM is just “inventory.” It isn’t. If you set it up only to list devices and never enforce policies or automate updates, you still have the same security risk you had before.
- Not standardizing config profiles. Without profiles, you end up with inconsistent states across machines and then automation doesn’t help.
What happens if you don’t do this right
Devices drift. Configs diverge. Security gaps appear. That’s when you get surprise breaches or compliance failures — and then you feel the cost of neglect.
2) Scalefusion Everyday Linux MDM
Scalefusion is a solid choice when you want straightforward, scriptable Linux device management with a focus on ease of use and remote control. It plays well with common distros like Ubuntu and Debian, however you will need to do extensive custom scripting to make it work in your linux environment.
Why use Scalefusion
If you’re not an enterprise yet but you have a fleet of Linux endpoints, think retail POS machines, remote worker laptops, or classroom devices. Scalefusion gives you central visibility and control. Policy management, remote terminal access, device grouping, all the basics are there. Scalefusion will not accept a meeting with you unless you have 50 devices, so keep that in mind.
How it works
Admin sets up a Scalefusion console. Endpoints enroll and check in. You push configs and scripts, monitor statuses, and troubleshoot.
You can also lock devices into kiosk mode — useful for dedicated purpose devices — and push updates remotely.
Common mistakes
- Underestimating ongoing maintenance: enrollment is easy, but you need a plan for updates, patching cadence, and retired devices.
- Ignoring reporting: Scalefusion gives you dashboard info — use it. If you ignore trends and logs, you’re flying blind.
Risks if done poorly
Endpoints aren’t just machines; they’re entry points into your network. Loose policies mean more attack surface.
3) SOTI MobiControl MDM with Field-Ready Tools
SOTI isn’t new, and its Linux support brings traditional enterprise mobility features remote diagnostics, geofencing, content distribution into the Linux space.
What it’s good for
If you’re managing Linux tablets, rugged devices, or remote field hardware, SOTI gives strong remote support and scheduling tools.
Common challenges
- Deployment complexity. Enterprise feature sets mean extra overhead.
- You need well-defined device roles and policies upfront or setup gets messy.
If you don’t use it right
You’ll have bots that aren’t managed consistently, and that means more break/fix calls and unpredictable uptime.
4) ManageEngine Endpoint Central
This is a unified endpoint management (UEM) suite with Linux support for patching, security enforcement, and remote control.
What it offers
- Patch management (huge for Linux).
- Asset discovery.
- App deployment automation.
- Remote support interfaces.
If your team already uses Endpoint Central for Windows or macOS, adding Linux is incremental and that lowers complexity.
Mistakes to avoid
- Treating it like a one-time install. UEM requires ongoing tuning to policy sets and update channels.
Outcome if neglected
You end up with unmanaged patches, outdated software, and a security team unhappy with you.
5) JumpCloud Identity-Centric MDM
JumpCloud shifts part of device management into identity and access control. It ties Linux device state to user policies and directory workflows.
When it shines
In cloud-native shops where access control is as important as device config. If you need single sign-on, remote patch workflows, and directory sync on Linux, JumpCloud puts those together.
How to do it right
Define clear identity policies first. Then link those to device management. JumpCloud becomes a central way to enforce who can do what and on which machine.
If you skip that
You get spotty policy enforcement and security gaps related to identity misuse.
6) SureMDM Limited Yet Practical Linux MDM
SureMDM is feature rich but easy to start with. It covers remote command execution, content filtering, kiosk mode, and policy management.
Why it matters
It’s practical. You deploy agents, manage from a single dashboard, and enforce both security and usability policies.
It supports a wide range of Linux types — servers, desktops, kiosks, embedded devices — without needing a bespoke setup for each.
Mistakes admins make
- Running only minimal policies because they don’t want to “disturb users.”
- Forgetting to set up monitoring alerts. If you only push configs and never check for compliance, you miss drift.
What happens then
You pay for hacks in time and stress later — devices silently falling out of compliance and nobody notices until it’s a fire drill.
7) Esper IoT / Embedded MDM
Esper shines if you’re managing embedded devices: kiosks, POS systems, wearables, custom Linux builds.
Esper gives you OTA updates, telemetry dashboards, and secure device provisioning.
When you use this
If your devices are built into hardware appliances or distributed geographically, Esper makes deployment and continuous updates scaled and automated.
Common misstep
Treating it like a desktop MDM. It’s not. You need to plan firmware and container workflows differently.
If you treat it like a general desktop tool, you’ll lose control of lifecycle updates and stability.
8) Open-Source Tools and DIY
There are open-source forks and lightweight agents that can give basic inventory and scripted config capabilities. But if you need compliance controls, you need Swif.
These are good for experimentation and internal tooling labs. But remember: without support, SLAs, and a roadmap, you’re owning all the risk. That’s fine if you’re prepared — but don’t pretend it’s “enterprise grade” without solid processes.
Linux MDM Reality Check: Practical Notes
MDM isn’t a silver bullet. It’s about process as much as software. Think about how you onboard and offboard employees, retrieve computers etc, the list goes on,
Why it matters
Linux endpoints are everywhere. Developers have them. Cloud engineers live in them. Kiosks and IoT devices run Linux. A breach on one device can be a beachhead into your network.
Linux MDM gives you:
- consistent configuration
- centralized control
- compliance reporting
- remote troubleshooting
- automated updates and policies
Common mistakes
- Treating it like a “set and forget” project.
- Ignoring reporting.
- Not planning for onboarding/offboarding devices.
- Overlooking identity integration.
What happens if you don’t do it right
You end up with:
- config drift
- security gaps
- compliance failures
- more manual work
- frustrated engineers
In short: Linux MDM isn’t optional for modern IT teams. It’s part of running reliable, secure, compliant infrastructure. The tools above range from unified enterprise platforms to lightweight, practical solutions. Pick the one that fits your actual needs, not the one with the flashiest marketing and treat implementation like a process, not a project.
If you want guidance on picking based on your specific environment, tell me a bit about your fleet and priorities, and we’ll walk it through together.